A B O U T
Most of my work has been to understand, create, invent, implement and test new methods of learning from data for important applications. I have been focused on computer security for the last two decades as “the killer app”. I’m driven to teach that securing large scale systems cannot be done without learning how to model the behavior of systems to detect bad behavior.
My career has been driven by one principle:
“Let the data speak the truth”.
I also believe Computer Science is still in its nascent formative years addressing many important questions. The principles of computer science ought to be taught to our children in their early education, to infuse algorithmic thinking to develop problem-solving skills necessary to solve a plethora of societal problems and issues. In our modern world, what isn’t the purview of computation? I’ll provide a post-it note to you for your answer.
I was born and raised in Brooklyn, New York, (to a blue collar immigrant family that I love and cherish) an oftentimes excuse for my clarity of message to (the chagrin of) my colleagues and friends.
_______
There is no beating around the bush in this Brooklyn-kid-gone-Ivy.
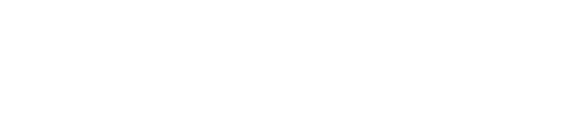
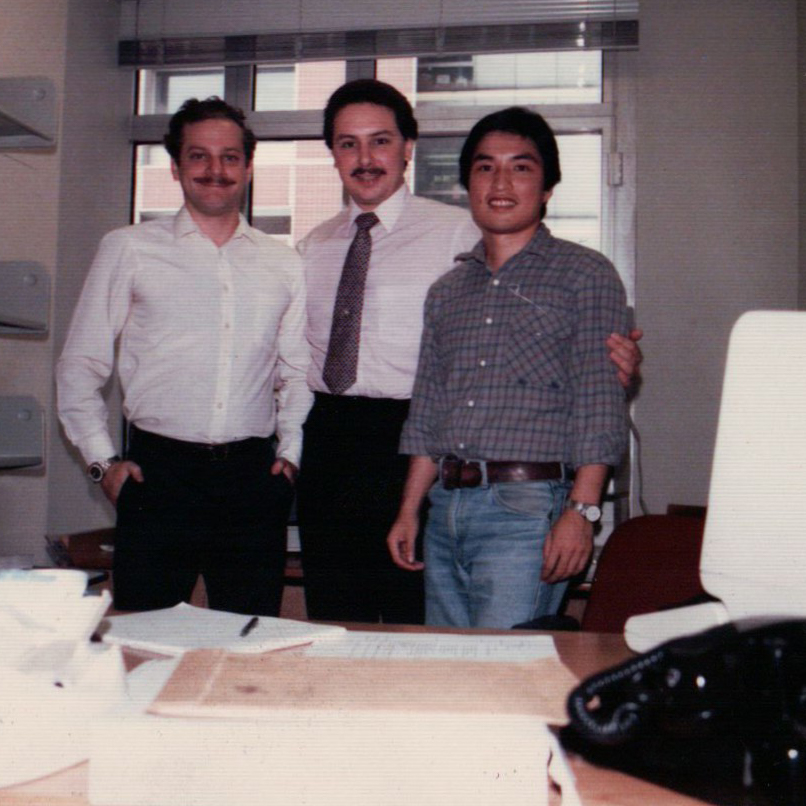
I am a product of New York City and its educational system as it was in the 1950’s. From Catholic School in Brooklyn, to CUNY Brooklyn College, then NYU, I’ve only seen the inside of New York classrooms. I was one of the few who graduated in 1979 (236 nationwide) with a PhD in Computer Science and I was barely older than a teenager. (Thank you New York City SP program for skipping 2 years of my schooling at the expense of proper maturation.) I charged ahead as an Assistant Professor at Columbia University. I learned nearly every stop on the IRT by the time I was 18. I also learned how never to be mugged or assaulted on the streets of my hometown. Thank you, Brooklyn. (I haven’t learned those lessons well in my academic home.)
MY CAREER HISTORY
Among the most important questions in science is “What is the universe made of”? I have been stuck on a different question for most of my life, “How has the universe become self-aware?” I hardly would touch the “why” part of that question. I thought Mathematical Logic was the key to approach this question.
I thought I would be a Logician until I experienced a CDC 6600 and a very odd programming language called LISP. It was easy to get hooked on Artificial Intelligence in those days, aided and abetted by Fortran, an extinct but elegant language called BALM (due to my advisor Malcolm Harrison) and SETL (due to my co-advisor Jack Schwartz). Did I mention “old school”? My PhD study was driven to understand how to “teach” a computer to play a child’s game. Machine learning caught my attention for quite some time to come. Then I fell into a mountain of data and realized machine learning applied to large amounts of data was a key enabler for so much discovery. Today, Data Science is the new term for an older pursuit.
My earliest work at Columbia focused on machine learning and large scale data analysis. I learned how real-world data is dirty and much needs to be done in order to effectively and efficiently learn from large-scale data. My earliest papers, some still often cited, dealt with hard problems in analyzing large amounts of data efficiently and with accuracy. The economics of life for a professor in those days forced me to consult and I soon was embedded in amazingly interesting work with the financial industry. I consulted with Citibank on their early fraud warning systems and that’s when I got hooked on learning to detect fraud.
_______
After working with large datasets of credit card transactions, I learned that humans are remarkably predictable - at least where money is concerned.
This lead to one of my major insights for security: your behavior can be modeled and used to predict what you are likely to do next. This intuition could be used to continuously test user’s to determine if they may have their credentials stolen by an impostor. By learning behavior of any system or user, one could protect systems from unknown attacks. This led to a major proposal I pitched to DARPA in 1996 on behavior-based security. The funding was used to start the Intrusion Detection Lab and my quest for pursuing machine learning applied to computer security. This has become widely known in the industry as user behavior analytics or behavioral biometrics, although it’s likely to change names again
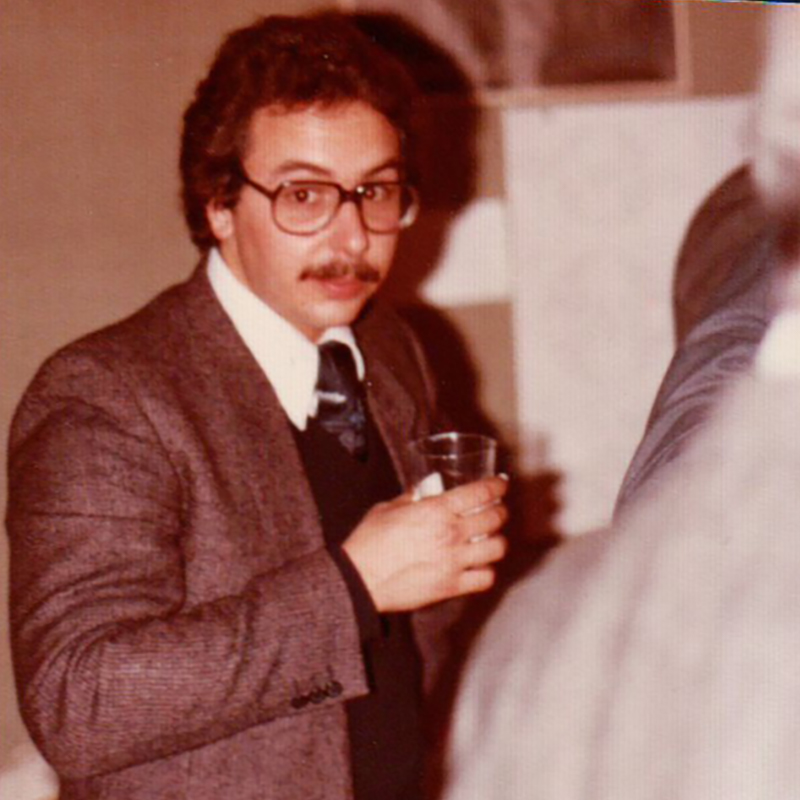
I also recognized that machines in the early 1980’s were just not capable of processing mountains of acoustic data, and so I embarked on building a 1K processor machine. The DADO machine executed pattern-directed inference computations at what was high-speed for that time. My phone computes faster today. (The killer app for DADO was Anti-Submarine Warfare by listening in parallel for a large number of acoustic samples of submarine hummings, but the open application was human speech keyword spotting. AT&T made use of our architecture for the first nation-wide automatic speech recognizer for operator switching.)
_______
Fraud detection research with Citibank led to my interest in developing automated machine learning infrastructures and applying this infrastructure to security problems. The JAM project (Java Agents for Meta-learning) was way ahead of its time.
Life expends considerable resource to secure itself and so must computer systems. It is only natural that living cells “learned” how to protect themselves, so should computers. Might we build computer systems that protect themselves from attack, unauthorized access, and misuse?I proposed that it could only be solved by machine learning methods and techniques applied to computer audit data. That has consumed my attention for decades. I happily sold DARPA on the idea that computer security research, and intrusion detection in particular, needed machine learning in order to keep up with the clever adversaries who were developing advanced attacks far faster than defenders could imagine. It seems most everyone in intrusion detection, academic and commercial, has agreed with this insight.
The Intrusion Detection Laboratory I established brought together a number of students and colleagues to work on some of the most pressing problems in security. Tens of millions of dollars, 107 patents, and two decades later, the IDS Lab has established a considerable body of new knowledge, as well as new technologies that are broadly used in modern security products and systems. There are many more to come that I am enthusiastically pursuing before I intentionally slow down and spend far more time on the science of security. Actually cybersecurity for quantum computing seems a quite interesting idea to think about. Imagine the bad guys ransoming a multi-billion dollar quantum computer? How might they do that?